North Koreans use fake names, scripts to land remote IT work for cash
 Send a link to a friend
Send a link to a friend
 [November 21, 2023]
By James Pearson [November 21, 2023]
By James Pearson
LONDON (Reuters) - Using fake names, sham LinkedIn profiles, counterfeit
work papers and mock interview scripts, North Korean IT workers seeking
employment in Western tech companies are deploying sophisticated
subterfuge to get hired.
Landing a job outside North Korea to secretly earn hard currency for the
isolated country demands highly-developed strategies to convince Western
hiring managers, according to documents reviewed by Reuters, an
interview with a former North Korean IT worker and cybersecurity
researchers.
North Korea has dispatched thousands of IT workers overseas, an effort
that has accelerated in the last four years, to bring in millions to
finance Pyongyang's nuclear missile program, according to the United
States, South Korea, and the United Nations.
"People are free to express ideas and opinions," reads one interview
script used by North Korean software developers that offers suggestions
for how to describe a "good corporate culture" when asked. Expressing
one's thoughts freely could be met with imprisonment in North Korea.
The scripts totaling 30 pages, were unearthed by researchers at Palo
Alto Networks, a U.S. cybersecurity firm which discovered a cache of
internal documents online that detail the workings of North Korea's
remote IT workforce.
The documents contain dozens of fraudulent resumes, online profiles,
interview notes, and forged identities that North Korean workers used to
apply for jobs in software development.

Reuters found further evidence in leaked darkweb data that revealed some
of the tools and techniques used by North Korean workers to convince
firms to employ them in jobs as far afield as Chile, New Zealand, the
United States, Uzbekistan and the United Arab Emirates.
The documents and data reveal the intense effort and subterfuge
undertaken by North Korean authorities to ensure the success of a scheme
that has become a vital lifeline of foreign currency for the
cash-strapped regime.
North Korea's U.N. mission did not respond to a request for comment.
Remote IT workers can earn more than ten times what a conventional North
Korean laborer working overseas in construction or other manual jobs
earns, the U.S. Justice Department (DOJ) said in 2022, and teams of them
can collectively earn more than $3 million a year.
Reuters was not able to determine how much the scheme has generated over
the years.
Some of the scripts, designed to prepare the workers for interview
questions, contain excuses for the need to work remotely.
"Richard", a senior embedded software developer, said "I (flew) to
Singapore several weeks ago. My parents got Covid and I (decided) to be
with family members for a while. Now, I am planning to go back to Los
Angeles in three months. I am thinking that I could start work remotely
right now, then I will be on board when I go back to LA."
A North Korean IT worker who recently defected also examined the
documents and confirmed their authenticity to Reuters: "We would create
20 to 50 fake profiles a year until we were hired," he said.
He viewed the scripts, data and documents and said it was exactly the
same thing he had been doing because he recognized the tactics and
techniques used.
"Once I was hired, I would create another fake profile to get a second
job," said the worker, who spoke on condition of anonymity, citing
security concerns.

In October, the DOJ and Federal Bureau of Investigation (FBI) seized 17
website domains it said were used by North Korean IT workers to defraud
businesses and $1.5 million in funds.
North Korean developers working at U.S. companies had hidden behind
pseudonymous email and social media accounts and generated millions of
dollars a year on behalf of sanctioned North Korean entities through the
scheme, the DOJ said.
"There is a risk to the North Korea government, as these privileged
workers are exposed to dangerous realities about the world and their
country's enforced backwardness," said Sokeel Park of Liberty in North
Korea (LINK), an organization that works with defectors.
[to top of second column]
|
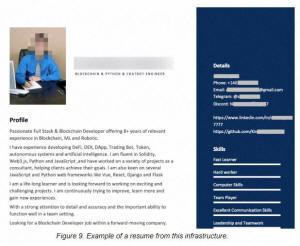
A redacted online resume of a North Korean IT worker is shown in
this screenshot of a report obtained by Reuters on November 20,
2023. U.S. cybersecurity research platform Palo Alto Networks Unit
42 /Handout via REUTERS
HARD CASH
Last year, the U.S. government said North Korean IT workers were
mainly located in China and Russia, with some in Africa and
Southeast Asia, and can each earn up to $300,000 annually.
According to his experience, the former IT worker said all are
expected to earn at least $100,000, of which 30-40% is repatriated
to Pyongyang, 30-60% spent on overhead expenses, and 10-30% pocketed
by workers.
He estimated there were around 3,000 others like him overseas, and
another 1,000 based within North Korea.
"I worked to earn foreign currency," he told Reuters. "It differs
between people but, basically, once you get a remote job you can
work for as little as six months, or as long as three to four
years."
"When you can't find a job, you freelance."
The researchers, part of Palo Alto's Unit 42 cyber research
division, made the discovery when examining a campaign by North
Korean hackers that targeted software developers.
One of the hackers left the documents exposed on a server, Unit 42
said, indicating there are links between North Korea's hackers and
its IT workers, although the defector said espionage campaigns were
for a select few: "Hackers are trained separately. Those missions
are not given to people like us," he said.
Still, there is crossover. The DOJ and FBI have warned that North
Korean IT workers may use access to hack their employers, and some
of the leaked resumes indicated experience at cryptocurrency firms,
an industry that has been long-targeted by North Korean hackers.
FAKE IDENTITIES
Data from Constella Intelligence, an identity investigation firm,
showed that one of the workers had accounts at over 20 freelancing
websites in the United States, Britain, Japan, Uzbekistan, Spain,
Australia and New Zealand.

The worker did not respond to an emailed request for comment.
The data, collated from leaks on the darkweb, also revealed an
account on a website selling digital templates to create
realistic-looking fake identification documents, including U.S.
driving licenses, visas and passports, Reuters found.
The documents unearthed by Unit 42 included resumes for 14
identities, a forged U.S. green card, interview scripts, and
evidence that some workers had bought access to legitimate online
profiles in order to appear more genuine.
The "Richard" in Singapore who was seeking remote IT work appeared
to refer to a forged profile by the name of "Richard Lee" – the same
name on the green card. The U.S. Department of Homeland Security did
not respond to a request for comment.
Reuters found a LinkedIn account for a Richard Lee with the same
profile photo who listed experience at Jumio, a digital identity
verification company.
"We do not have any records of Richard Lee having been a current or
former employee of Jumio," a Jumio spokesperson said. “Jumio does
not have any evidence to suggest the company has ever had a North
Korean employee within its workforce.”
Reuters messaged the LinkedIn account seeking comment, but received
no response. LinkedIn removed the account after receiving requests
from Reuters for comment.
"Our team uses information from a variety of sources to detect and
remove fake accounts, as we did in this case," a spokesperson said.
(Reporting by James Pearson; Additional reporting by Ted Hesson and
Daphne Psaledakis in Washington; Editing by Chris Sanders and Anna
Driver)
[© 2023 Thomson Reuters. All rights
reserved.]This material
may not be published, broadcast, rewritten or redistributed.
Thompson Reuters is solely responsible for this content. |